
Privacy by Design (PbD) is a term from the General Data Protection Regulation (GDPR), which many organizations have probably heard of. It is a mandatory element when processing personal data, which revolves around attention to data protection in the design phase of a product or service. However, Privacy by Design is still quite a challenge for many organizations because it often remains too abstract and theoretical. In this article we explain why Privacy by Design is important for every organization, what the 7 principles of Privacy by Design mean, and we show how you can apply the theory in practice.
What is Privacy by Design and why is it important?
Privacy by Design originated in the early 1990s and is an engineering and strategic management approach that allows you to minimize information system’s privacy risks selectively and sustainably through technical and organizational controls. The concept of privacy by design was developed around 1990 by Ann Cavoukian, then information & privacy commissioner in Ontario, Canada. She believes that privacy should be embedded into information technologies (IT), business practices, and networked infrastructures, as a core functionality.
By thinking about this beforehand, organizations can avoid encountering challenges related to the processing of personal data later on. The fact is that Privacy by Design has only become more relevant in recent decades. The amount of data inside and outside your organization is growing exponentially. As a result, it is becoming increasingly complex to keep control over which personal data you process and to identify and prevent challenges in an early stage, instead of repairing them afterwards.
Implementing Privacy by Design not only helps you to keep control over which personal data you process and to identify and prevent challenges in an early stage, it also helps in repairing them afterwards. It also allows you to work in a cost-efficient manner. Since you include technical and organization controls to mitigate privacy risks in an early design stage, which prevents that you have to make expensive adjustments later on while developing a product or service, for example. Operationalizing Privacy by Design can even help you gain a competitive advantage because if you protect and respect your customer’s privacy (even) better, this will build trust and loyalty with the result that customers become ambassadors for your brand.
The Principles of Privacy by Design
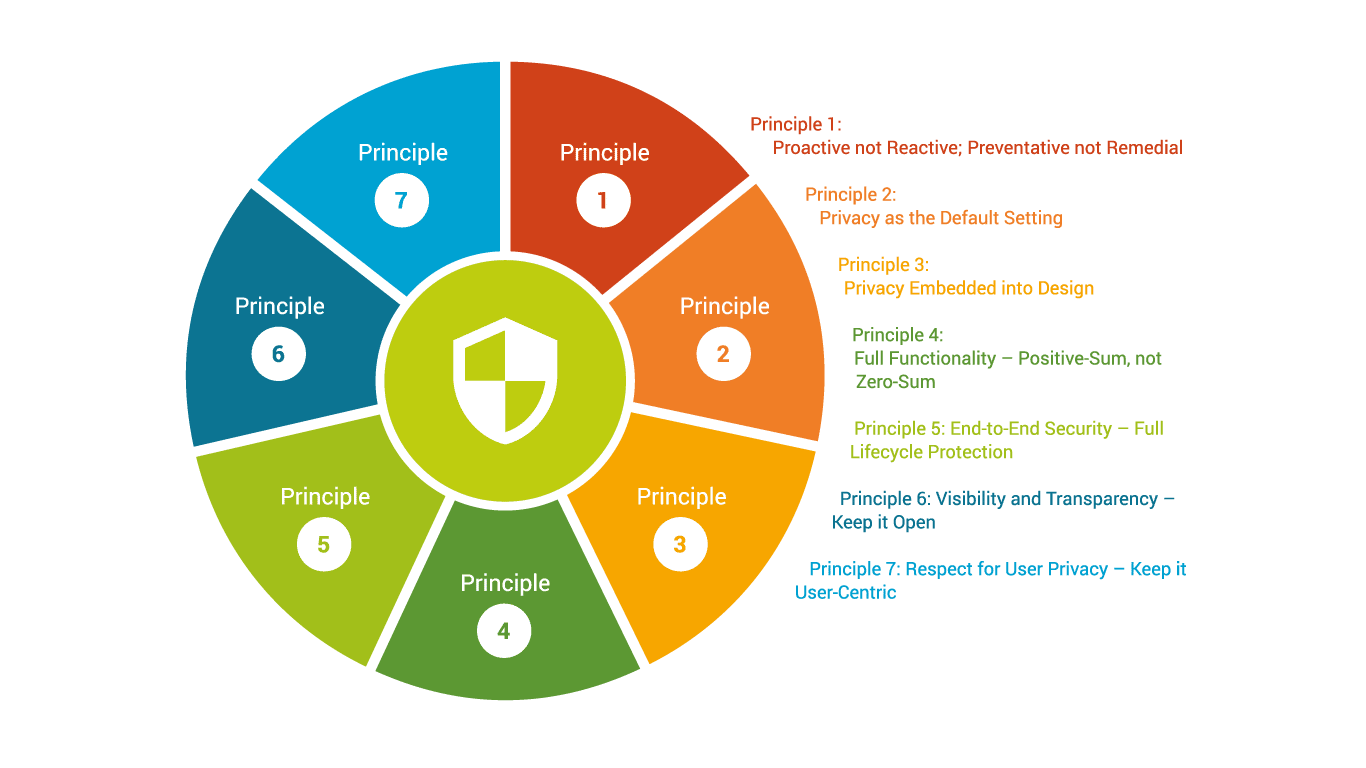
To understand how Privacy by Design works, it is useful to know which 7 Fundamental Principles the theory contains. The practical outcome of the implementation of the principles can vary within each organization and strongly depend on the specific circumstances. We will briefly explain each principle to give you a basic understanding of how to integrate this data protection concept into your company.
 1. Proactive not Reactive; Preventative not Remedial
1. Proactive not Reactive; Preventative not Remedial
The first principle includes the importance of having a proactive and not a reactive approach in any product, service, system or process. The aim should be to prevent that privacy risks will materialize. Privacy by Design expects you to anticipate and implement proactive measures to prevent privacy invasive events from occurring, instead of offering remedies for solving such events.
2. Privacy as the Default Setting
The second principle is about setting privacy as the default setting. Users need to be able to trust one thing – the default settings. As a starting point, organizations can provide maximum privacy assurance to personal data in any of their IT systems or business process without any further action that is needed on the side of the individual whose data is being processed.
3. Privacy Embedded into Design
The basis of this principle is that privacy should be included as an essential component in the design and architecture of IT systems and business operations. This means that privacy should be included from the very beginning in which core functionality is delivered, and not something you include as an ‘add-on’ in a later stage of the design process.
4. Full Functionality – Positive-Sum, not Zero-Sum
This principle aims to accommodate legitimate interests and objectives in a ‘win-win’ manner, rather than an approach that makes unnecessary compromises with privacy. It rejects the zero-sum view that privacy should be sacrificed if you are aiming for other design objectives, legitimate interests, and/or technical capabilities. It stimulates a positive-sum approach in which you will have a doubly-enabling outcome with privacy in mind.
5. End-to-End Security – Full Lifecycle Protection
The goal of the fifth principle is to ensure that data is secured and destroyed in a timely manner throughout the entire lifecycle management. Throughout its entire lifecycle data should be secured from end-to-end, at rest, in transit, and while in use. Furthermore, this should be consistent with international standards that have been developed and recognized.
6. Visibility and Transparency – Keep it Open
It is very important that the technology or business practice involved is transparent to the user, that it is aligned with the objectives that are stated and shared with individuals, and that it is subjected to independent verification.
7. Respect for User Privacy – Keep it User-Centric
This principle focuses on measures in an information system that are strong privacy defaults, appropriate notice and empowering user-friendly options to keep it user-centric. This means that a system should be designed for the user, anticipating his or her privacy perceptions, needs, requirements, and default settings.
An example of an organization that applies Privacy by Design
By understanding which principles there are, you can also better apply them in practice. For your inspiration, we will show you an example of an organization that has applied Privacy by Design in their own way. This is an existing company, but for privacy reasons we do not use their real name.
A large car manufacturer is looking at launching a new online web shop that offers a variety of car parts and accessories to consumers. Their current web shop is not functioning properly and is outdated, so they would therefore like to improve it. The organization has gathered a project team that besides the project team leader, consists of members of several departments, such as IT, marketing, and logistics. The project members were aware that they should also consider privacy and therefore consulted their Data Privacy Officer (DPO) about this matter. Their DPO advised to include the privacy officer in the project team to make sure that they correctly apply Privacy by Design. Luckily for them, they did not start the project yet so the privacy officer could be included from the very beginning of the project. In addition, they decided to set up a privacy governance team with people with diverse expertise and, above all, senior leadership. In this case, the Chief Legal Officer was appointed as the direct line between the team and the board. To ensure that employees receive appropriate training, a program was set up for privacy training that suits the role and responsibilities of different employees.
An example of a Privacy by Design framework in 5 steps
1 step: understanding functionalities
The starting point for the project team was to ensure that the privacy of their end users (customers) is protected when creating the web shop. That is why they have opted for a layered approach to better understand the functionalities for the user. The team developed a policy in which privacy expertise is included early in the development of engineering processes or system development. The policy includes important elements, such as purpose, retention term, data minimization and security measures.
2 step: assessing risks and securing personal data
When designing the website, the project team thought carefully about how to secure the collection, storage and processing of personal data. Customers’ personal information is stored and processed in a separate database system. This system uses encryption keys that are of a sufficient length at different levels, depending on the nature of the data. In addition, before the launch of the web shop, a risk assessment is performed on the IT infrastructure, to allow the organization to ensure that it works as expected before it is going live. After the go live, this check is performed periodically.
3 step: unified user experience
A user-centric identity management system was implemented for unified User Experience for different services (from desktop to mobile phones). In every environment, end users are informed about their privacy rights under the GDPR and the obligation from article 13. Via a plugin, an online form is used to point out to the user his or her data subject rights, such as the right to access, deletion or correction of data.
4 step: keeping insight in data collection
To establish Privacy as the Default Setting, the team developed a record of processing activities to keep insight into exactly which data is collected within the web shop environment. Clear agreements have been made, stating that the collection of personal information is kept to a strict minimum. Where information is collected for analysis, it is continuously monitored with data governance tooling who has access to that data and what is done with it. Furthermore, the website developer has been instructed to apply the most privacy-friendly settings in the application. Information is published in the web shop environment about the way in which the company processes personal data and how they handle security. The contact details of those responsible for privacy and security are also included in the attached policies.
5 step: getting started
As you have read, applying Privacy by Design is quite possible in every organization. The subject seems very abstract to many organizations, but it can be a useful way of working to think carefully about the data privacy of your end users when developing new products and services. So don’t let the theory stop you from getting started.
 1. Proactive not Reactive; Preventative not Remedial
1. Proactive not Reactive; Preventative not Remedial